Top 10 Patch Management Best Practices for Enhanced Security
For 25 years, Camwood has helped enterprises optimise their IT estate by up to 95% and reduce operational costs by up to 40%. Our Fusion Framework delivers clean, ready-to-innovate data, streamlined user experiences and measurable, sustainable growth, truly taking you beyond applications.
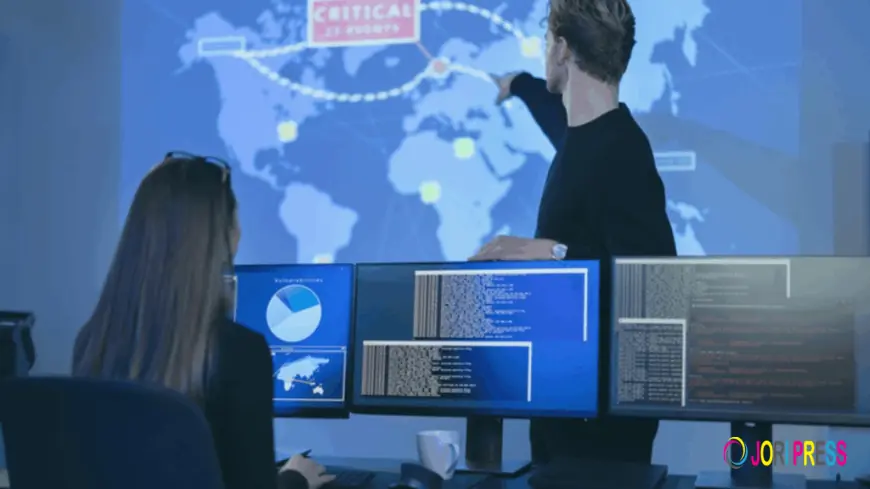
Eighty-five per cent of ransomware attacks target known vulnerabilities that already have patches available.
The implication is stark: most breaches are not the result of sophisticated zero-day exploits or nation-state attacks beyond your control. They are the result of patch management discipline failures the gap between a patch becoming available and that patch being deployed.
The top 10 patch management best practices that follow are the operational foundation of a genuinely secure enterprise estate. They are not aspirational ideals. They are the specific disciplines that consistently produce 95%+ compliance rates, sub-4-hour zero-day response times, and measurable reductions in breach probability across financial services, healthcare, manufacturing, aerospace, and government organisations.
This guide goes deeper than a high-level overview. Each practice includes the security rationale, the implementation reality, and where relevant the specific failure mode that organisations experience when the practice is absent.
The Top 10 Patch Management Best Practices for Enhanced Security
1. Establish Complete Asset Visibility Before Patching Anything
Security outcome: Eliminate the unknown attack surface that attackers exploit whilst defenders focus on known systems.
You cannot protect what you cannot see. This principle is obvious in theory and consistently violated in practice. Organisations conducting their first thorough estate inventory discover surprises without exception: shadow IT devices connected to the network, acquired company tenants with unmanaged estates, legacy applications running on forgotten servers, firmware on networking equipment that has never been patched.
One organisation discovered 847 applications across their estate where they expected approximately 300. Another found 47 end-of-life applications across recently acquired tenants three had critical vulnerabilities actively being exploited in the wild at the time of discovery.
Advanced discovery tools using ALICE complete comprehensive estate mapping devices, operating systems, applications, firmware versions, end-of-life status within one day. Manual methods take months and leave gaps. Complete, continuously updated asset visibility is the non-negotiable foundation for every practice that follows.
Implementation priority: Before any other investment in patch management capability.
2. Implement Risk-Based Patch Prioritisation Using Multiple Intelligence Sources
Security outcome: Address genuinely dangerous vulnerabilities first, rather than vendor-labelled priorities that overstate urgency across the board.
'We have 200 vulnerabilities marked critical. Which do we patch first?'
Every security leader faces this problem. Scanners flag hundreds of issues simultaneously. Vendors mark almost everything critical. Without an intelligent triage framework, teams either attempt everything (and achieve little) or default to arbitrary prioritisation.
Effective risk-based patch prioritisation integrates four intelligence sources:
- CVSS severity scores — technical baseline assessment
- Active exploitation intelligence — is this vulnerability being actively used by attackers right now? CISA's Known Exploited Vulnerabilities catalogue is an authoritative source
- Business criticality — which systems are most critical to operations, revenue, or patient safety?
- Compensating controls — what mitigations are already in place that reduce effective risk?
A CVSS 9.8 vulnerability on an internally-facing development system with no internet exposure may be less urgent than a CVSS 7.2 vulnerability on an internet-facing payment processing system actively being exploited in the wild. Risk-based prioritisation makes this distinction explicit.
3. Define Emergency Response Protocols Before You Need Them
Security outcome: Compress zero-day response time from days to hours by eliminating crisis-time decision ambiguity.
The zero-day announcement arrived at 4:47pm on a Friday. An aerospace manufacturer with 8,000 endpoints needed to protect critical systems before the Monday morning exploitation window opened. Organisations with pre-defined emergency protocols had critical systems patched within 3 hours. Organisations relying on ad hoc crisis decisions were still in approval conversations Monday morning.
Effective zero-day patch management best practices require documenting before the crisis:
- Who has emergency deployment authority and at what thresholds
- Which system categories are prioritised for immediate action
- What testing is required vs. waived for emergency deployments
- Stakeholder notification procedures and communication templates
- Pre-approved deployment windows that can be activated without standard change management
Organisations that reduce zero-day response from 8-12 days to under 4 hours do so through preparation, not resources. The resources are the same. The preparation is different.
4. Automate Testing Environments That Mirror Your Production Configuration
Security outcome: Prevent patch-induced outages that cause organisations to delay or avoid patching, creating persistent vulnerability exposure.
The most common reason organisations delay patching is fear of operational disruption. A patch breaks an application dependency. A driver update causes system instability. An update conflicts with a bespoke configuration. These outcomes are real, and they create a rational reluctance to patch promptly.
Automated testing environments that replicate production configuration eliminate this barrier. Every patch is validated against your specific applications, drivers, and configurations before enterprise deployment catching compatibility conflicts, performance impacts, and application-specific issues that generic vendor testing does not account for.
Every deployment should include:
- System snapshots before deployment (enabling one-click rollback)
- Tested compatibility with business-critical applications
- Performance baseline comparison post-patch
- Automated regression testing for critical workflows
Testing infrastructure is not a luxury. It is the mechanism that allows organisations to patch confidently and promptly.
5. Deploy in Phases Using Controlled Rollout Strategies
Security outcome: Eliminate the all-or-nothing risk of enterprise-wide simultaneous deployments whilst maintaining momentum.
Phased patch deployment means structured progression through deployment stages, each acting as a validation gate before proceeding:
- Pilot groups (5-10% of estate): representative systems from different business units and configurations
- Canary deployments: gradual expansion with automated monitoring for anomalies
- Blue-green deployments: zero-downtime patching maintaining parallel environments for critical systems
- Rolling deployments: incremental updates for high-availability infrastructure
A problematic patch that reaches 5% of your estate creates a manageable incident. The same patch reaching 100% of endpoints simultaneously creates a crisis that takes days to resolve and teaches the organisation that patching is dangerous, reinforcing the avoidance behaviour that leaves systems vulnerable.
Phased deployment and comprehensive testing (Practice 4) work together: testing catches issues in controlled environments; phased rollout catches issues that only emerge at scale.
6. Integrate Vulnerability Intelligence Directly Into Patch Prioritisation Workflows
Security outcome: Ensure the most actively exploited vulnerabilities are addressed first, reducing actual breach probability rather than nominal compliance metrics.
Patch management without vulnerability intelligence is patching against a static list. Vulnerability intelligence integration means patch prioritisation decisions are informed by real-time data on active exploitation, threat actor activity, and emerging attack patterns.
The integration creates a continuous loop:
1. Vulnerability scanner identifies unpatched CVEs across the estate
2. Threat intelligence enriches each CVE with active exploitation status
3. Business criticality weighting is applied to affected systems
4. Prioritised patch queue is generated and fed into deployment workflow
5. Post-deployment verification confirms closure of each vulnerability
This integration is the subject of its own discipline. (→ See Blog 2: The Difference Between Patch Management and Vulnerability Management for the complete integration framework.)
7. Maintain Tested Rollback Procedures for Every Deployment
Security outcome: Remove the operational fear of patching that causes organisations to accept persistent vulnerability exposure.
Organisations without patch rollback capability face an impossible choice when a patch causes unexpected issues: accept the operational instability, or manually reverse changes across hundreds or thousands of endpoints a multi-day effort that consumes the team and delays the next patch cycle.
This impossible choice teaches organisations that patching is dangerous. The behavioural result is delayed patching, exception proliferation, and a growing pool of unpatched vulnerabilities.
Automated rollback capabilities system snapshots before every deployment, automated rollback triggers on defined failure conditions, one-click restoration for individual devices or groups transform this dynamic. Patching becomes a routine operation with a known, manageable downside, rather than a high-stakes event to be avoided.
Rollback procedure requirements:
- Pre-deployment system snapshot for every deployment
- Defined rollback trigger conditions (application failure, performance degradation)
- Tested restoration procedures (not theoretical ones)
- Maximum rollback time SLA (target: under 30 minutes for critical systems)
8. Implement Real-Time Compliance Dashboards Across Regulatory Frameworks
Security outcome: Transform compliance from a periodic, resource-intensive exercise into continuous, automated governance.
GDPR, ISO 27001, NIST 800-53, SOC 2, PCI DSS, HIPAA, and Cyber Essentials all require demonstrable, documented patch management processes. Manual compliance evidence gathering exporting reports, correlating data across tools, preparing audit packs—consumes significant IT resource and produces evidence that is out of date before it is reviewed.
Real-time compliance dashboards provide:
- Device-level patch status: which devices are compliant, non-compliant, or in exception
- Framework-specific views: compliance status mapped to each regulatory requirement
- Business unit breakdowns: visibility by department, location, or system type
- Audit-ready evidence packs: automated report generation on demand
One CISO discovered 47 end-of-life applications across acquired tenants during a systematic compliance review, three of which had active exploits in the wild. The result: £4.2 million in potential GDPR fines avoided through proactive remediation before a breach occurred.
Patch compliance best practices require this visibility to be continuous not just available during audit preparation.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0