How Endpoint Security Protects Businesses from Cyber Threats

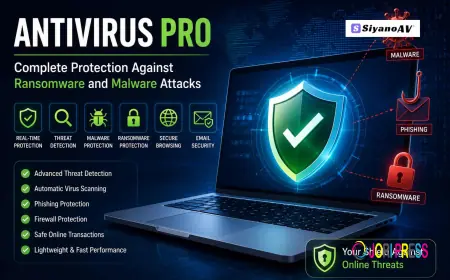
In today’s digital environment, businesses rely heavily on connected devices such as laptops, desktops, smartphones, and servers to operate efficiently. While these devices improve productivity and communication, they also create potential entry points for cybercriminals. Hackers often target these endpoints to gain access to sensitive company data and networks. This is why Endpoint Security has become a critical component of modern cybersecurity strategies.
Organizations of all sizes face increasing cyber threats, including ransomware attacks, phishing scams, malware infections, and data breaches. By implementing strong Endpoint Security, businesses can protect their devices, networks, and valuable information from these growing threats.
Understanding Endpoint Security
Endpoint Security refers to the practice of securing devices that connect to an organization's network. These endpoints may include employee laptops, mobile devices, tablets, and even IoT devices. Since each device acts as a gateway to the company’s network, it is essential to protect them against unauthorized access and malicious attacks.
Modern Endpoint Security solutions go beyond traditional antivirus software. They include advanced technologies such as threat detection, behavioral analysis, device monitoring, and automated response mechanisms. These tools help organizations identify potential risks and stop attacks before they spread across the network.
Why Cyber Threats Target Endpoints
Endpoints are often the weakest points in a company’s security infrastructure. Employees use these devices daily for browsing the internet, sending emails, downloading files, and accessing cloud applications. This constant activity creates opportunities for cybercriminals to exploit vulnerabilities.
Without proper Endpoint Security, a single infected device can give attackers access to an entire corporate network. This could allow them to steal confidential information, install malware, or disrupt business operations.
Businesses that rely on remote work are especially vulnerable, as employees often connect to corporate systems from different locations and networks. This makes strong endpoint protection even more important.
How Endpoint Security Protects Businesses
1. Protection Against Malware and Ransomware
One of the main benefits of Endpoint Security is its ability to detect and block malware before it infects a system. Malware can enter devices through email attachments, malicious websites, or compromised software downloads.
Advanced security tools analyze files and applications in real time to identify suspicious behavior. If malware is detected, the system automatically blocks the threat and prevents it from spreading to other devices.
2. Real-Time Threat Detection
Cyber threats are constantly evolving, and traditional security tools may not always detect new attack methods. Modern Endpoint Security solutions use artificial intelligence and machine learning to identify unusual activities and potential threats.
These systems monitor device behavior continuously and alert security teams if suspicious actions occur, allowing businesses to respond quickly and minimize potential damage.
3. Protection for Remote Work Environments
Remote and hybrid work environments have significantly increased the number of endpoints connected to corporate networks. Employees often access company systems using personal devices and unsecured internet connections.
Implementing effective Endpoint Security ensures that devices remain protected regardless of where employees are working. Security policies, encryption, and remote monitoring help maintain strong protection even outside the office network.
4. Data Protection and Access Control
Sensitive business information must be protected from unauthorized access. Cybercriminals often attempt to steal financial data, intellectual property, or customer information from compromised devices.
Strong Endpoint Security includes access control policies that limit who can view, modify, or share specific data. These controls help prevent both accidental data leaks and intentional data theft.
5. Centralized Security Management
Managing security across multiple devices can be challenging for IT teams. Modern Endpoint Security platforms provide centralized dashboards that allow administrators to monitor and control all connected devices from one location.
This centralized approach helps organizations quickly identify vulnerabilities, apply security updates, and respond to threats across the entire network.
6. Compliance with Data Protection Regulations
Many industries must follow strict data protection regulations to safeguard customer information. Failure to comply with these regulations can lead to significant legal penalties and reputational damage.
By implementing strong Endpoint Security, organizations can ensure that devices handling sensitive data follow proper security policies and compliance standards.
The Role of AI in Endpoint Security
Artificial intelligence is playing a major role in improving cybersecurity technologies. AI-powered security systems can analyze large volumes of data to detect hidden threats and unusual patterns that may indicate cyberattacks.
Platforms like IDox Ai are helping organizations enhance their cybersecurity frameworks by integrating intelligent monitoring and automated security capabilities. AI-driven solutions improve threat detection accuracy and reduce response times when security incidents occur.
These advanced technologies allow businesses to stay ahead of evolving cyber threats while maintaining efficient operations.
Best Practices for Strengthening Endpoint Security
To maximize the effectiveness of Endpoint Security, businesses should follow several best practices.
First, organizations should keep all devices updated with the latest security patches and software updates. Many cyberattacks exploit outdated systems with known vulnerabilities.
Second, companies should implement strong authentication measures such as multi-factor authentication. This ensures that only authorized users can access company systems and sensitive information.
Third, employee training is essential. Many cyberattacks begin with phishing emails or social engineering tactics that trick employees into revealing sensitive information. Educating staff about cybersecurity risks can significantly reduce these threats.
Finally, businesses should regularly monitor their networks and conduct security audits to identify potential vulnerabilities before attackers can exploit them.
Conclusion
Cyber threats continue to evolve, making it essential for businesses to adopt advanced security strategies to protect their digital assets. Devices connected to corporate networks are often targeted by attackers, making them a critical focus for cybersecurity efforts.
By implementing effective Endpoint Security, organizations can detect threats early, protect sensitive data, and maintain secure business operations. These solutions help businesses safeguard their networks against malware, ransomware, and other cyberattacks.
With innovative security technologies and intelligent protection systems from providers like IDox Ai, businesses can build a stronger defense against modern cyber threats and ensure their digital environments remain secure.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0