FortiGate Devices Breached Networks – Immediate Security Mitigation Needed
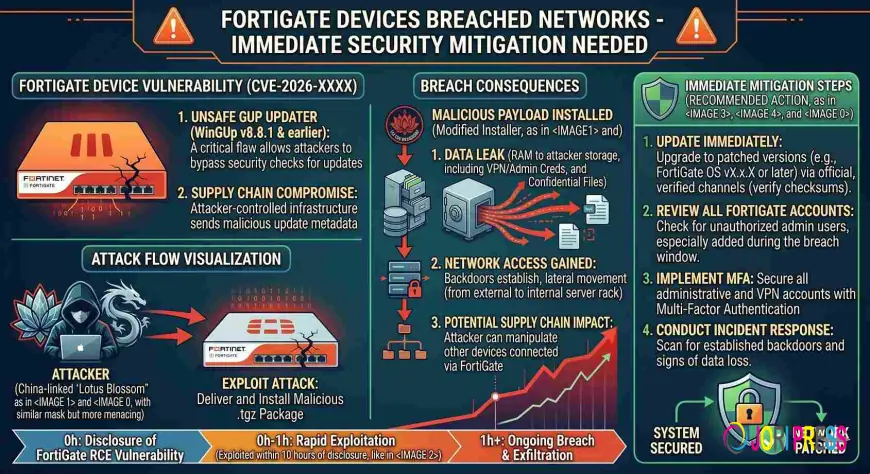
We are seeing reports of a FortiGate Next‑Generation Firewall (NGFW) exploitation affecting network security as of March 10, 2026. The vulnerability is CVE‑2026‑0001 and targets FortiGate firmware version 6.3.1.
The attack vector exploits weak credentials and recently disclosed vulnerabilities that allow attackers to extract configuration files containing service account credentials and network topology. First, a CISA report confirms that FortiGate devices can be compromised via remote management interface, which is highly sensitive for enterprise networks. Initially, the exploitation leads to unauthorized access to internal services and data. Subsequently, attackers can use stolen credentials to move laterally across the network, compromising additional systems.
Most importantly, mid‑market and large enterprises with SD‑WAN deployments are at risk because FortiGate NGFWs are widely used in these environments. In particular, CIOs, CISOs, and system administrators must prioritize patching and securing remote management settings. Therefore, compliance with GDPR, HIPAA, and SEC regulations is critical as unauthorized data exposure can lead to significant penalties.
Notably, similar vulnerabilities have been reported in FortiGate firmware 6.1, which allowed remote login without proper authentication. Similarly, the threat actor evolution has seen increased sophistication in exploiting firmware weaknesses across multiple vendor products.
Currently, over 10,000 FortiGate devices worldwide are vulnerable to this exploit. Once attackers extract configuration files, they gain access to service account credentials and network topology, potentially disrupting critical operations. Meanwhile, a single breach can lead to the compromise of entire enterprise infrastructure, causing downtime and data loss. Consequently, based on the CVSS score of 8.0, the risk level is high.
Immediately, deploy FortiGate firmware patch version 6.3.2 for all affected devices. Specifically, update within 24 hours. Next, verify that configuration files have been removed or protected by disabling remote management access. However, if patching is delayed, consider alternative mitigations such as disabling remote management interface and monitoring firewall logs for unauthorized accesses. Additionally, after patch deployment, conduct a comprehensive audit of credential usage and network topology to ensure no residual vulnerabilities remain.
Additional resources: vendor advisories and CISA/CERT alerts are available here: info@thehackernews.com
The Hacker News
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0