Compliance and IT Security: Meeting Modern Regulations
In today’s digital-first environment, compliance and IT security are no longer separate concerns; they are deeply interconnected. As organizations handle increasing volumes of sensitive data, governments and regulatory bodies around the world are introducing stricter laws to ensure that information is properly protected. Businesses that fail to meet these requirements risk not only financial penalties but also long-term reputational damage.
In today’s digital-first environment, compliance and IT security are no longer separate concerns; they are deeply interconnected. As organizations handle increasing volumes of sensitive data, governments and regulatory bodies around the world are introducing stricter laws to ensure that information is properly protected. Businesses that fail to meet these requirements risk not only financial penalties but also long-term reputational damage.
Modern regulations are designed to enforce accountability, transparency, and security across industries. From data privacy laws to sector-specific cybersecurity standards, organizations must navigate a complex regulatory landscape. This requires a proactive approach where compliance is built into IT security strategies rather than treated as an afterthought.
Staying ahead of evolving regulations and cybersecurity standards is critical for long-term business success. As IT environments become more complex, businesses need smarter ways to manage compliance alongside security operations.
Solutions like FutureFeed are designed to bridge this gap by delivering real-time insights, automation, and streamlined workflows that help organizations stay aligned with modern compliance requirements while improving overall security posture.
Understanding the Link Between Compliance and IT Security
Compliance refers to adhering to laws, regulations, and industry standards that govern how data is managed and protected. IT security, on the other hand, focuses on safeguarding systems, networks, and data from unauthorized access or breaches. While these concepts serve different purposes, they are closely aligned.
Without strong IT security measures, compliance cannot be achieved. Similarly, compliance frameworks often provide structured guidelines that help organizations implement effective security practices. This overlap makes it critical for businesses to integrate both functions into a unified strategy.
Key Regulations Shaping IT Security in 2026
Organizations must comply with a variety of regulations depending on their industry and geographic reach. Some of the most influential regulatory frameworks include data protection laws, financial security standards, and healthcare regulations.
Common Regulatory Requirements
|
Requirement |
Description |
|
Data Encryption |
Protecting data during storage and transmission |
|
Access Control |
Limiting system access to authorized users |
|
Incident Reporting |
Timely reporting of data breaches |
|
Data Minimization |
Collecting only necessary information |
|
Audit and Monitoring |
Continuous tracking of system activity |
These requirements are designed to reduce risk and ensure that organizations are prepared to respond effectively to security incidents.
The Cost of Non-Compliance
Failing to meet regulatory standards can have serious consequences for businesses. Financial penalties are often the most immediate impact, but they are far from the only concern.
Organizations may also face legal action, loss of customer trust, and operational disruptions. In some cases, non-compliance can even lead to restrictions on business operations, especially in regulated industries like finance and healthcare.
Impact of Non-Compliance
|
Consequence |
Impact Level |
|
Financial Penalties |
High |
|
Legal Consequences |
Severe |
|
Reputation Damage |
Critical |
|
Operational Downtime |
Moderate |
These risks highlight the importance of treating compliance as a core business priority rather than a secondary obligation.
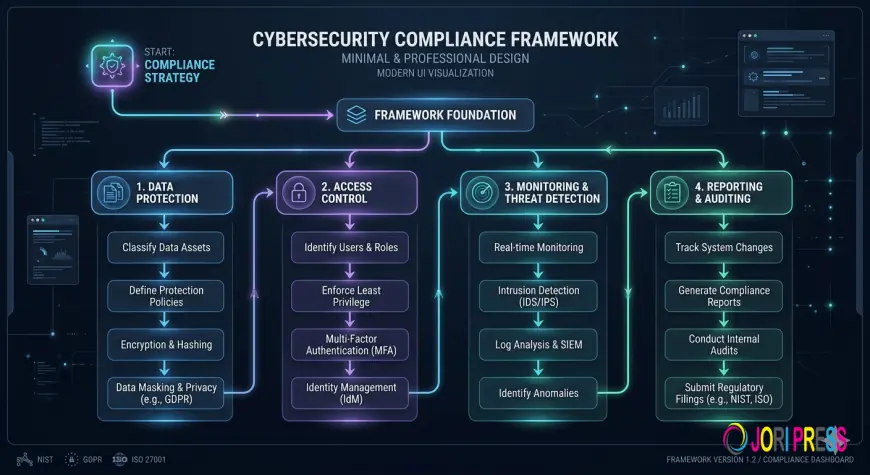
Building a Compliance-Driven Security Strategy
To effectively meet modern regulations, businesses must adopt a structured approach to IT security. This involves aligning security practices with compliance requirements and ensuring that all systems and processes are designed with protection in mind.
A strong compliance-driven strategy typically includes risk assessments, policy development, and the implementation of advanced security tools. Organizations must also ensure that employees understand their role in maintaining compliance, as human error remains a significant risk factor.
Role of Technology in Compliance
Technology plays a crucial role in helping organizations achieve and maintain compliance. Advanced tools can automate many aspects of security, reducing the likelihood of human error and improving efficiency.
For example, security information and event management (SIEM) systems can monitor network activity in real time, while automated compliance tools can generate reports and track adherence to regulatory standards. Encryption technologies, identity management systems, and endpoint security solutions also contribute to a more secure and compliant environment.
Challenges Businesses Face
Despite the availability of advanced tools and frameworks, many organizations struggle with compliance. One of the biggest challenges is the constantly evolving nature of regulations. Keeping up with changes requires continuous monitoring and adaptation. Another major challenge is the complexity of modern IT environments. With the widespread use of cloud services, remote work, and third-party integrations, maintaining visibility and control over all systems can be difficult.
“Compliance is not a one-time achievement but an ongoing process that requires continuous improvement and vigilance.”
Additionally, smaller businesses often lack the resources and expertise needed to implement comprehensive compliance strategies, making them more vulnerable to both cyber threats and regulatory penalties.
Best Practices for Meeting Modern Regulations
Organizations can improve their compliance posture by adopting a set of best practices that align with both security and regulatory requirements.
Key Practices
-
Conduct regular risk assessments to identify vulnerabilities
-
Implement strong access controls and authentication mechanisms
-
Encrypt sensitive data both at rest and in transit
-
Maintain detailed logs and monitoring systems
-
Provide ongoing cybersecurity training for employees
These practices not only help businesses meet regulatory requirements but also strengthen their overall security posture.
The Future of Compliance and IT Security
As technology continues to evolve, so will the regulatory landscape. Emerging technologies such as artificial intelligence, blockchain, and the Internet of Things are introducing new challenges and opportunities for compliance.
Regulators are expected to introduce more stringent requirements to address these advancements, making it even more important for businesses to stay agile. Organizations that invest in scalable security solutions and maintain a proactive approach to compliance will be better positioned to adapt to future changes.
Conclusion
Compliance and IT security are no longer optional; they are essential components of modern business operations. Meeting regulatory requirements requires more than just following rules; it demands a comprehensive approach that integrates security into every aspect of the organization.
By understanding the relationship between compliance and IT security, leveraging the right technologies, and adopting best practices, businesses can reduce risk and build a strong foundation for long-term success. In an increasingly regulated world, those who prioritize compliance will not only avoid penalties but also gain a competitive advantage through trust and reliability.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0